Description
Course Overview
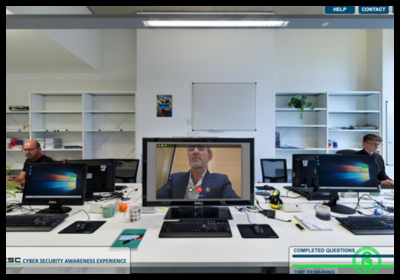
In this Escape Room cybersecurity training experience, you’ll enter a virtual, but entirely recognisable office environment. You will play the character of Alex, a regular office worker focused on getting your day job done. You’ll receive some training in the Knowledge Hub, and then back to your desk for the first of a series of scenarios – some of which are indeed cyber-attacks, but some are just business as usual.
You’ll work through a sequence of 27 scenarios, making decisions and receiving feedback. And in the background, you’ll be scored, to find out whether you’re a budding cyber expert or maybe need to go again.
Course Content
You’ll start in the Knowledge Hub, where you will receive awareness training on common cyber-attacks, such as:
- Phishing for theft of information or installation of malware
- Ransomware
- MFA attacks
- Brute Force MFA attacks, and more.
And receive some best practice guidance on protecting yourself, such as the use of strong passwords, recognising red flags, secure browsing and the importance of software updates. And guidance on what to do and who to turn to if something goes wrong.
And then into action with 27 scenarios, mixing cyber-attacks with some harmless business-as-usual situations. Interacting with your colleagues, your boss, visitors, telephone and video conference calls, and emails, of course, on your desktop and mobile device. You’ll receive feedback on all decisions – if you made the wrong choice, you’ll get guidance on what you might do differently next time and why. And if you made a good choice, that will be explained to.
Your responses will be tracked, resulting in an overall score that you will receive at the end.
The course is designed and intended to be completed in a single sitting (if you break off, you will need to start again). You can repeat the experience as many times as you like.
Learning objectives
By the end of the Cyber Security Escape Room training, participants should be able to:
- Identify common cyber threats such as phishing, malware, social engineering, and password attacks. Phishing is the most common method used by cybercriminals to gain unauthorized access to systems and information.
- Apply best practices for online security, including creating strong passwords, recognizing suspicious emails, and safeguarding personal information. Weak passwords are a leading cause of data breaches, and email scams are increasingly used to trick individuals into revealing sensitive details such as bank information.
- Understand the importance of data protection and the consequences of data breaches. Businesses have a responsibility to ensure employees are aware of cybersecurity risks and good practices, as data breaches can have serious operational, financial, and reputational impacts.
- Recognize the role of individual responsibility in maintaining cyber safety within an organization or community. Cyber-attacks can have devastating consequences – some businesses have been forced to downsize or even close because of attacks.
Entry requirements
There are no entry requirements.
Course assessment and certification
On successful completion of all the tasks and the final assessment, you will be able to download your certificate.







 UK: 0844 854 9218 | International: +44 (0)1488 580017
UK: 0844 854 9218 | International: +44 (0)1488 580017